What Is a Reverse Proxy? A Technical Overview
A reverse proxy is a type of server that sits in front of a web server to act as an intermediary between clients and this web server. It intercepts requests coming from clients and then forwards them to the backend web server, allowing for more traffic control and providing additional security and performance benefits.
In this article, we’ll explain how a reverse proxy works and what benefits it adds to a web application architecture. We’ll also cover some of the implementation patterns of a reverse proxy, and we’ll highlight some of the most well-known reverse proxy software and services.
How a Reverse Proxy Works
The main role of a reverse proxy is to reduce direct exposure of web servers (also called origin servers) to the clients. It acts as a middleman that receives the client requests and then forwards them to the server.
It also receives response traffic and forwards it to the clients on behalf of the server, preventing the clients and the server from having a direct connection.
Now let’s understand this process in more detail.
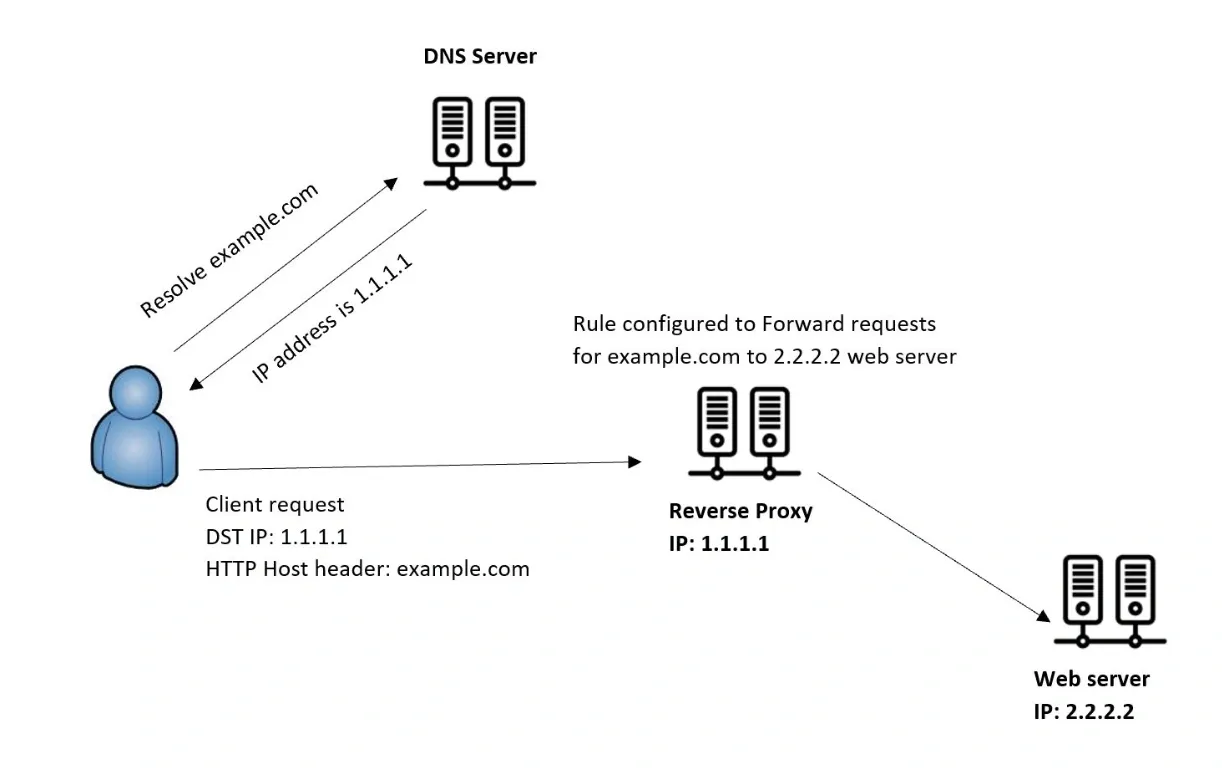
When a client sends a request to the web server, we need to get it routed to the reverse proxy first, and not directly to the server. This is commonly achieved via DNS by resolving the website's domain name to the reverse proxy server's IP address instead of the web server's. Traffic can also be routed through a load balancer, CDN, or WAF.
After the reverse proxy receives the client request, it decides to forward it to the backend web server based on some rules that are configured on the reverse proxy.
Technically speaking, a reverse proxy operates at layer 7 of the OSI model, specifically the HTTP protocol, although some can also proxy at the transport layer (TCP/TLS). When operating at layer 7, the reverse proxy rules will control the routing decisions, often based on HTTP attributes (host/path/headers) inside the request. When a matching rule is detected, the request is routed based on this rule. We can also configure rules on the reverse proxy to block some requests, adding an additional layer of security to our architecture.
Why Use a Reverse Proxy
Adding the extra layer of a reverse proxy before a web server is a very common pattern, and it brings a lot of benefits, including:
- Security & Traffic filtering: As the reverse proxy sits in front of the web server, it helps reduce direct exposure of origin IPs when the origin is locked down, hiding the real identity of the server. This makes it very difficult for attackers to target the web server directly, because all they can see as the destination of the connection is the reverse proxy itself, which typically has very strong security measures in place, although it can still be targeted by a DDoS attack. Additionally, we can configure reverse proxy rules to filter and block specific traffic based on certain criteria, allowing for even more security and control.
- Load balancing & High availability: A reverse proxy can also distribute incoming traffic to multiple origin servers, not only one, making the website or service capable of handling higher traffic load. This also serves as a high-availability architecture, so that if one of the web servers stops working, the reverse proxy can route the traffic to the rest of the servers that are still running.
- Caching: When a web server responds to a client request through a reverse proxy, the reverse proxy can also cache the response data. This allows subsequent client requests for the same data to be served much faster from the cached content, improving the overall performance of the website.
- SSL/TLS offloading: Instead of executing the SSL/TLS encryption and decryption on the web server itself, which consumes a lot of its resources as it’s a computationally heavy process, we can offload this to the reverse proxy, freeing up the web server resources for handling the actual client requests, which improves the performance. TLS termination also centralizes certificate management and can reduce load on origin servers, though performance gains depend on traffic and hardware.
Where Can Reverse Proxies Be Used
As we saw, using reverse proxies can bring a lot of advantages, this made them a good fit for many use cases and encouraged their adoption in different architectures, such as the following:
- Web apps & APIs: Web applications are considered the main use case for reverse proxies, it’s the most common pattern for deploying a reverse proxy when it’s placed in front of one or more web servers. Reverse proxies can also be deployed in front of backend APIs. This can also be achieved by creating forwarding rules on the reverse proxy that route the API requests to the backend service.
- E-commerce & High-traffic sites: The performance benefits that reverse proxies bring from things like load balancing, SSL termination, or content caching make them a perfect addition to high-traffic websites like e-commerce. These websites also require high security measures in place, so they also benefit from the security features of the reverse proxies.
- Multi-server and multi-region deployments: Multi-server & multi-region deployment is an architecture where multiple application servers are distributed across multiple geographical locations to serve clients from different regions. In such deployments, reverse proxies can load-balance incoming client requests more efficiently by forwarding requests to the server closest to the client, reducing latency and improving application performance.
This technique is also sometimes called global server load balancing (GSLB). Global routing can also be handled by a CDN or global load balancer (GeoDNS/Anycast). In that scenario, reverse proxies typically load-balance within a region; multi-region often uses a global front door plus regional reverse proxies.
How are Reverse Proxies Often Implemented?
Reverse proxies can be implemented in many different patterns depending on the requirements that need to be satisfied. Let’s explore some of the most common patterns for implementing reverse proxies.
Single Web App Behind One Proxy
The most standard implementation pattern for a reverse proxy is adding a single web application behind a single reverse proxy server. In this pattern, the reverse proxy server acts as a single entry point to the web app, and the rules configured on the reverse proxy are set to forward requests only for this web application.
This pattern is simple to implement and enhances the security of the web application by hiding the original IP address of the backend web server, filtering traffic, and using SSL/TLS. It can also improve performance if caching is enabled and multiple backend servers are added to serve the web app, along with the reverse proxy load balancing.
The main architecture components in this pattern are the reverse proxy server, which is the publicly facing component that receives the incoming requests from the client, and the backend web servers, which are hidden behind the reverse proxy and run the actual application.
API Gateway Pattern
An API gateway can also act as a reverse proxy by serving as an intermediary between client requests and backend services, and offering features like traffic routing, load balancing, and security. However, API gateways are considered more specialized and typically provide additional API management capabilities.
While a reverse proxy is more general-purpose, API gateways can handle some API-specific tasks like API version management, request transformation, authentication, authorization, rate limiting, and protocol translation. Additionally, configuring an API gateway is usually more complex than configuring just a dedicated reverse proxy.
The pattern of using an API gateway as a reverse proxy makes more sense if you already need the additional specialized API management features that it provides, but if you only need to implement a reverse proxy, it’s much more reasonable to use a dedicated reverse proxy service.
CDN Pattern
A CDN is a geographically distributed network with servers placed at edge locations closer to users. These edge servers act as reverse proxies by hiding the origin servers behind them, receiving the client requests on their behalf, and then forwarding the requests to the backend origin servers. They become the public front-facing entry point for the application, providing typical reverse proxy benefits like security, availability, and load balancing.
CDNs can also dramatically improve application performance by caching content from origin servers, taking advantage of the CDN’s geographical distribution, which allows the cached content to be served from the closest location to the user, reducing latency and boosting application responsiveness.
In a typical CDN pattern, an automatically generated domain name is offered by the CDN provider, which is associated with your created CDN distribution and resolved to the specific edge servers. When you have your own custom domain name that you want to associate with your web app, you typically create a CNAME record that links your custom domain name to the CDN-provided domain name.
Reverse Proxy Software and Managed Services
There are different options available for deploying a reverse proxy. You can install the reverse proxy software on your own servers, allowing you to have total control over the underlying infrastructure, but adding more overhead for the management and administration.
Another option is to use a managed service, which means that the reverse proxy service is running on a provider’s infrastructure, which you don’t need to manage yourself, offloading the additional effort of infrastructure management to the provider itself and allowing you to focus on configuring the service.
Now, let’s highlight some of the most used reverse proxy software and services.
Self-Hosted Reverse Proxy Software
Starting with the reverse proxy software that you deploy yourself and host on your own infrastructure, here are some of the most widely used ones:
- Nginx: Known for its high performance and the ability to serve heavy-traffic websites, Nginx is a reverse proxy and web server software that’s reliable, secure, and has a massive community support. It is originally an open-source software that’s free to use, but it also has a commercial version called Nginx Plus that’s developed by F5.
- HAProxy: HAProxy is a powerful reverse proxy and load balancer that’s capable of handling both HTTP and TCP traffic. It provides reliable and fast load balancing with complex load balancing algorithms, which makes it very suitable for high-availability architectures.
- Apache: The Apache HTTP server is also a very common option for running a reverse proxy. It can work as a reverse proxy and provide the different reverse proxy features through multiple modules, including mod_proxy, mod_proxy_http, mod_proxy_balancer, and mod_ssl.
- Traefik: Traefik is a cloud-native, modern reverse proxy that is designed to work with containers and microservices and provides a lot of configurations that fit these environments. It offers easy and seamless integration with different container orchestration tools like Kubernetes and container engines like Docker.
Managed Reverse Proxy Services
As we mentioned, managed services remove the administration and maintenance overhead of the underlying infrastructure as the service provider handles these parts. This makes the provisioning and setup of the reverse proxy much easier and faster.
Some of the well-known managed reverse proxy services include:
- Cloudflare CDN: The Cloudflare CDN is a globally distributed network of servers that allows caching content near client locations to reduce latency and improve performance. It acts as a reverse proxy by sitting between clients and the origin servers. It receives the client requests at the edge locations and routes them to the destination service, hiding the real identity of the backend server. It also offers security and high-availability features like SSL/TLS termination, DDoS protection, and load balancing.
- Amazon Cloudfront: Cloudfront is Amazon’s CDN service with a massive geographical distribution and global presence. Similar to Cloudflare CDN, it also works as a globally distributed reverse proxy that receives client requests and forwards them to the backend origin servers while offering load balancing, caching, and security features.
- Azure Front Door: Front Door is a cloud-based CDN that is geographically distributed through Microsoft’s global edge network and points-of-presence, allowing optimized and secure access to your content and applications. Its massive scale helps improve performance by delivering content from edge locations closer to the users, reducing required direct access to origin servers with each request.
Reverse Proxy vs Forward Proxy, Load Balancer, CDN, and VPN
Reverse proxies are capable of providing different features that can overlap with other services that offer similar features in a more dedicated fashion. So, in this section, we’re going to compare reverse proxies with other technologies that have some similarities with them.
|
Feature |
Reverse Proxy |
Forward Proxy |
Load balancer | CDN | VPN |
|---|---|---|---|---|---|
| Main Function |
Intermediary between clients and web servers to protect web servers and hide their identity |
Protects clients and filters their outgoing traffic when accessing internet resources | Distribute traffic across multiple target servers | Caches content in edge locations geographically closer to the clients | Secures the client connection to a network |
| Main Benefits |
Security, performance, and high availability |
Security, Bypassing restrictions, content filtering | Performance, high availability | Content caching, performance | Security |
| Location | In front of web servers | In front of clients | In front of servers | Geographically distributed on edge locations | Between clients and the network |
| IP masking |
Hides the server IP |
Hides the client IP | Hides the server IP | Hides the server IP | Hides the client IP |
| Key Use Case | Securing Web Servers | Filtering corporate user traffic | Distribute traffic | Caching static content | Client remote access |
Reverse Proxy Security Vulnerabilities & Implementation Risks
Deploying a reverse proxy needs a keen eye on detail because if not done properly, it can lead to security, availability, or performance issues. Let’s check some of the risks in implementing a reverse proxy:
- Misconfiguration Vulnerabilities: If the rules on the reverse proxy are not configured correctly, it can expose the origin servers to targeted attacks or allow unintended access, bypassing the reverse proxy security controls.
- Single Point of Failure: The reverse proxy should be the main entry point to access the backend origin servers, so if it goes down or stops running, the whole web application can become unavailable.
- Software Vulnerabilities: The reverse proxy software needs to be updated frequently to avoid any known vulnerabilities that can be exploited by attackers.


